This is the third part in the Citrix Configuration Logging Series. In part 1, we discussed what Citrix Configuration Logging was. In part 2, we discussed how to prepare the database to log configuration changes. In this part, we will discuss how to set up the Citrix XenApp farm to use the database and what happens under the covers when we do this.
Configuring the Citrix XenApp Farm to use the Database
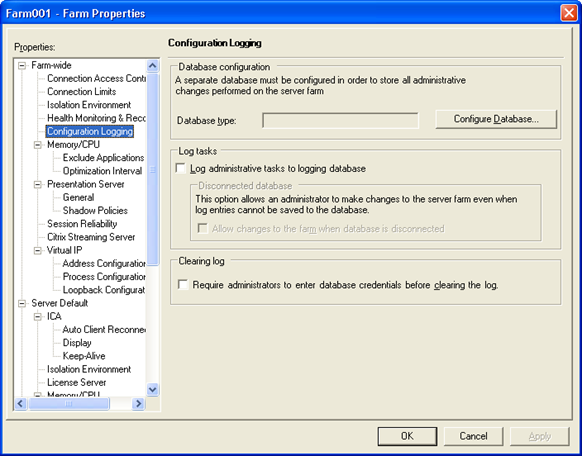
You use the Access Management Console to configure the XenApp farm for Configuration Logging. Configuration Logging is a farm setting, so once you open the Access Management Console, simply right-click your farm name and select “Properties”. Select “Configuration Logging” from the Farm-wide properties.
Now, we need to point our farm to the database we created before. To do this, click the “Configure Database…” button to start the database configuration wizard.
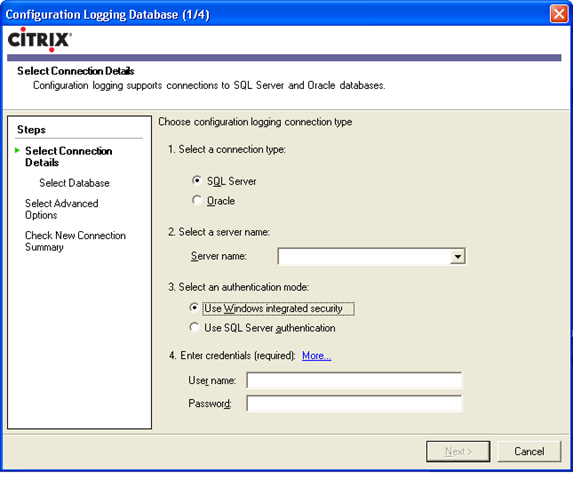
The screen shot above is pretty self-explanatory, but here are a couple of tips:
- Even though there is a drop down next to the “Server name” box, the discovery does not always work. I suggest just typing in the database server name or IP address.
- Be sure to specify server\instance if you are not using the default database instance.
- If using Windows integrated security, type domain\username in the “User name” field
- Keep in mind that the username and password is saved in the data store. So, be sure that the password does not expire, or remember to change this when the password does expire.
- Discovery does not work well with the database name on the next step either. Again, you will most likely have to type in the database name.
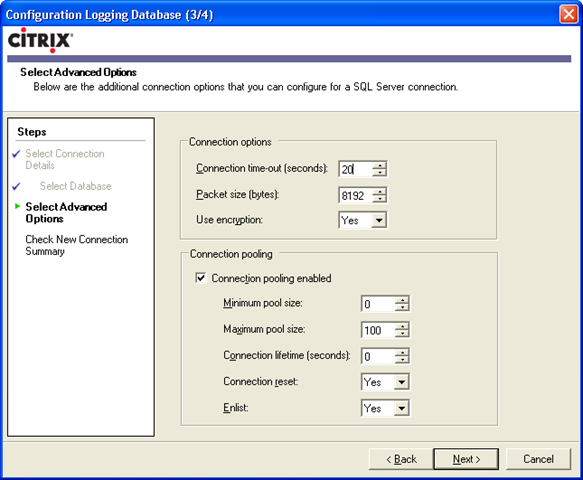
The screen shot above shows a lot of settings, but there is not a lot of explanation of what these settings do. Remember, Configuration Logging is built on top of ADO.NET. In order to make sense of these settings, you can look at ADO.NET properties. So, here ya go:
- Connection time-out (seconds) – amount of time to wait for a command to execute. If a database write command cannot execute in 20 seconds, you’ve got a problem.
- Packet size (bytes) – the size of the network packet. 8192 is the default. This value can be anywhere from 512 to 32767.
- Use encryption – more on this in a minute…
- Connection pooling enabled – connection pooling is just like session sharing. Building up and tearing down database connections can be an expensive process. Connection pooling allows a connection to stay up for an amount of time before closing just in case another database request comes in. If another database request comes in before the time out, the request will use the same connection.
- Minimum pool size – specifies the minimum number of connections to maintain in a pool. If you set this number to 3, for example, ADO.NET would create 3 connections the first time you connect to the server. Zero is the ADO.NET default.
- Maximum pool size – maximum number of connections in a pool. 100 is the ADO.NET default.
- Connection lifetime (seconds) – specifies the maximum age of connections. If a connection has been open for more than this number of seconds when you call its Close() or Dispose() method, it will be destroyed rather than being returned to the pool. Zero is the ADO.NET default, which means that connections are kept in the pool regardless of age.
- Connection reset – specifies whether the database connection is reset when being removed from the pool. True is the ADO.NET default.
- Enlist – specifies whether to enlist this connection into a current transaction context of the creation thread. In other words, if this is set to true and the database server is doing some transactions, let the connection use the already generated transaction. True is the ADO.NET default.
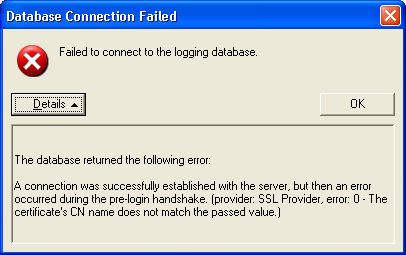
Almost all of those defaults are just great. The only one you need to be careful about is the “Use encryption” option. This option is set to “Yes” by default. But, in order to use Configuration Logging encryption, you must be using IMA encryption. If you are not using IMA encryption, you cannot use Configuration Logging encryption. You will get this nasty undescriptive error when you test the connection if there is a mismatch:
For information on how to setup IMA encryption, check out the Citrix XenApp documentation.
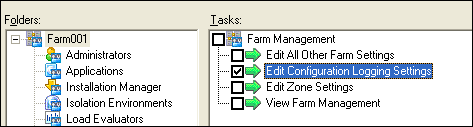
Configuring the Citrix XenApp farm to Log Changes
Now that we have the farm configured to point to the database, we have some options on how to log changes. Remember this screen shot?
This is pretty easy, there are only 3 checkboxes:
- Log administrative tasks to logging database – this is what tells the IMA service to use the
CitrixLogServer.dllhook to log changes explained in part 1. - Allow changes to the farm when database is disconnected – this is self explanatory.
- Require administrators to enter database credentials before clearing the log - “the log” referred to in this option is all the data in the database. An administrator can clear the log by opening the AMC, right-clicking on the farm name - > All Tasks –> Clear configuration log.
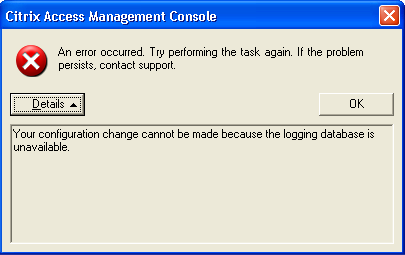
If you do not allow changes to be made to your farm and your Configuration Logging database is offline, you will get the following error message when trying to make a change:
Wow – that error message is actually pretty descriptive!
Note – even if you do not allow changes to be made to your Citrix XenApp farm when the Configuration Logging database cannot be reached, you can still change which database your farm uses. That means if you are trying to make a change and your database took a dive and it doesn’t look like it will be back up anytime soon, you can always change which database logs the changes and carry on. Of course, changing which database logs changes gets logged <- say that 5 times fast…
Adjusting Database Permissions
As you may recall, when we created the data base user in part 2, we had to make sure the database user belonged to the db_owner role. This is due to the fact when the XenApp farm connects to the database, the schema is checked. If the schema does not exit, it is created – which requires db_owner rights. So, after that first connection, you can dial back the permissions. Here are the minimum operating permissions:
| Configuration Logging Task | Database permissions needed |
| To create log entries in the database tables | INSERT for the database tables, EXECUTE for the stored procedures, and SELECT for sysobjects and sysusers (SQL Server) or sys.all_objects (Oracle) (Oracle also requires SELECT for sequence objects and the create session system privilege) |
| To clear the log | DELETE/INSERT for the database tables, EXECUTE for the GetFarmData stored procedure, and SELECT for sysobjects and sysusers (SQL Server) or sys.all_objects (Oracle) (Oracle also requires SELECT for sequence objects and the create session system privilege) |
| To create a report | EXECUTE for the Citrix Configuration Logging stored procedures SELECT for sysobjects and sysusers (SQL Server) or sys.all_objects (Oracle) (Oracle also requires the create session system privilege) |
Delegated Administration
Delegated administration is supported to an extent. It is basically an on or off thing. It is a good idea to make sure administrators have to enter credentials to clear the log as well.